Run KAI for continuous coverage. Bring in our operators for the engagements AI shouldn't run alone. Most teams do both.
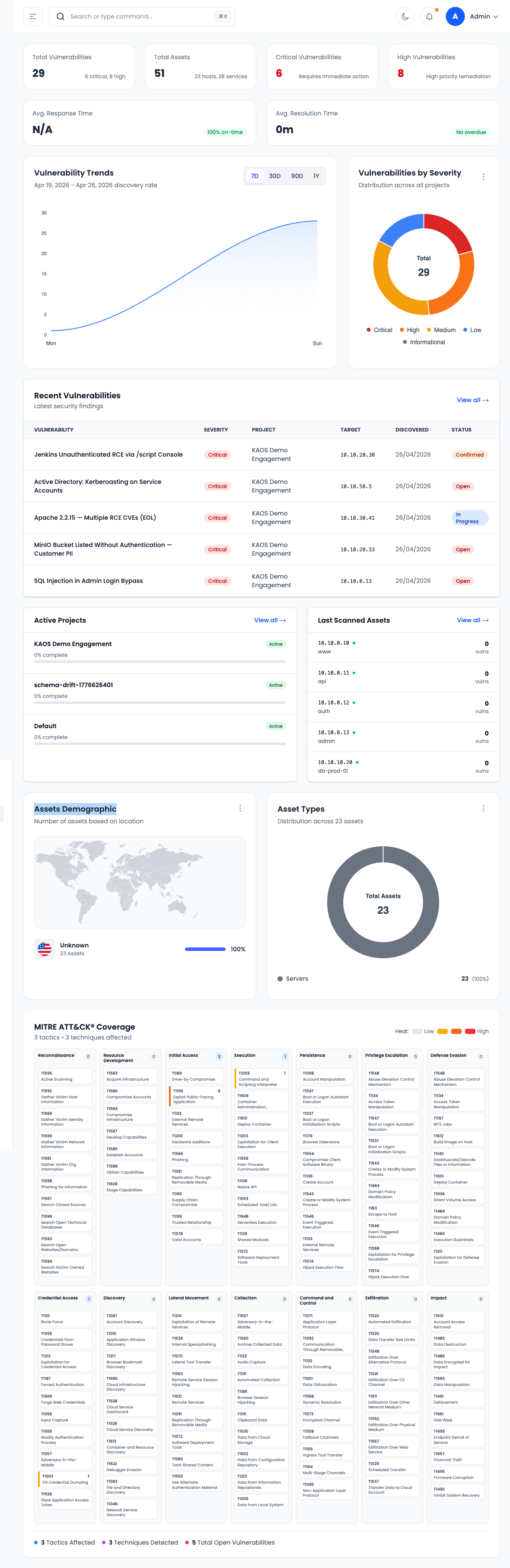
Autonomous AI agent that finds and exploits real vulnerabilities 24/7. Continuous testing, real-time alerts, compliance reporting.
Certified offensive security experts. Manual pentesting, compliance audits, and red team operations with decades of combined experience.
Watch KAI run recon, exploit, validate, and ship the report — on a real target, in one pass.
Live walkthrough scheduled monthly. Want a private one? Book 15 minutes.
Six numbers from real engagements. None are projections.
See How KAI Works →Across all engagements
Continuously updated
Discovered by our team
Every finding ships with reproduction steps
While humans focus on the hard cases
On a typical engagement
Six security leaders. Three engagements that replaced existing pentest contracts.
We used to chase 800 scanner findings a quarter. With KAOS, we get 30 — and every single one is reproducible. My engineers stopped resenting security.
The proof-of-exploitation reports went straight into our SOC 2 audit package. Our auditor specifically asked who built them. That's how good they are.
We pay for managed pentests every year. KAOS is the first vendor that actually finds chained vulnerabilities a tool would never spot — and writes them up like a senior pentester.
Quotes used with permission. Full case studies under NDA — request access.
OSCP, OSCE3, CREST and CRTO operators running engagements with C2 frameworks we built ourselves and tooling tuned against current EDR detections.
Deep-dive security assessments that go beyond automated scanning. Business logic flaws, chained exploits, and creative attack paths only humans can find.
Full-scope adversary simulation using self-designed C2 frameworks and custom tooling built to bypass modern defenses.
Phishing campaigns, vishing, and physical security assessments that test your organization's human attack surface.
Line-by-line security review of your codebase by experienced developers who think like attackers.
Collaborative exercises where our red team works alongside your blue team to improve detection, response, and overall security posture in real time.
Deep forensic analysis of compromised systems, evidence preservation, and root cause investigation to understand exactly what happened.
Our team publishes original security research — from zero-day discoveries to AI-driven vulnerability analysis. Born from years of hands-on offensive security work, we share what we learn to advance the cybersecurity community.
From CVE disclosures to deep-dive technical analysis, our research directly feeds into KAI — making it smarter with every finding.
View All Research & Blog Posts →One target. 24 hours. A reproducible exploit — written by KAI, reviewed by an OSCE3 operator. No card, no signup.







