Built by Security Practitioners
Designed and trained by certified offensive security operators — OSCP, OSCE3, CRTO. The human pedigree the agent inherits.
Trained on OSCP / OSCE3 / CRTO Methodology
KAI was designed and trained by offensive security professionals holding OSCP, OSCE3, and CRTO certifications. The agent reasons the way a senior pentester does — methodology first, tools second.
Real Exploitation, Real Impact
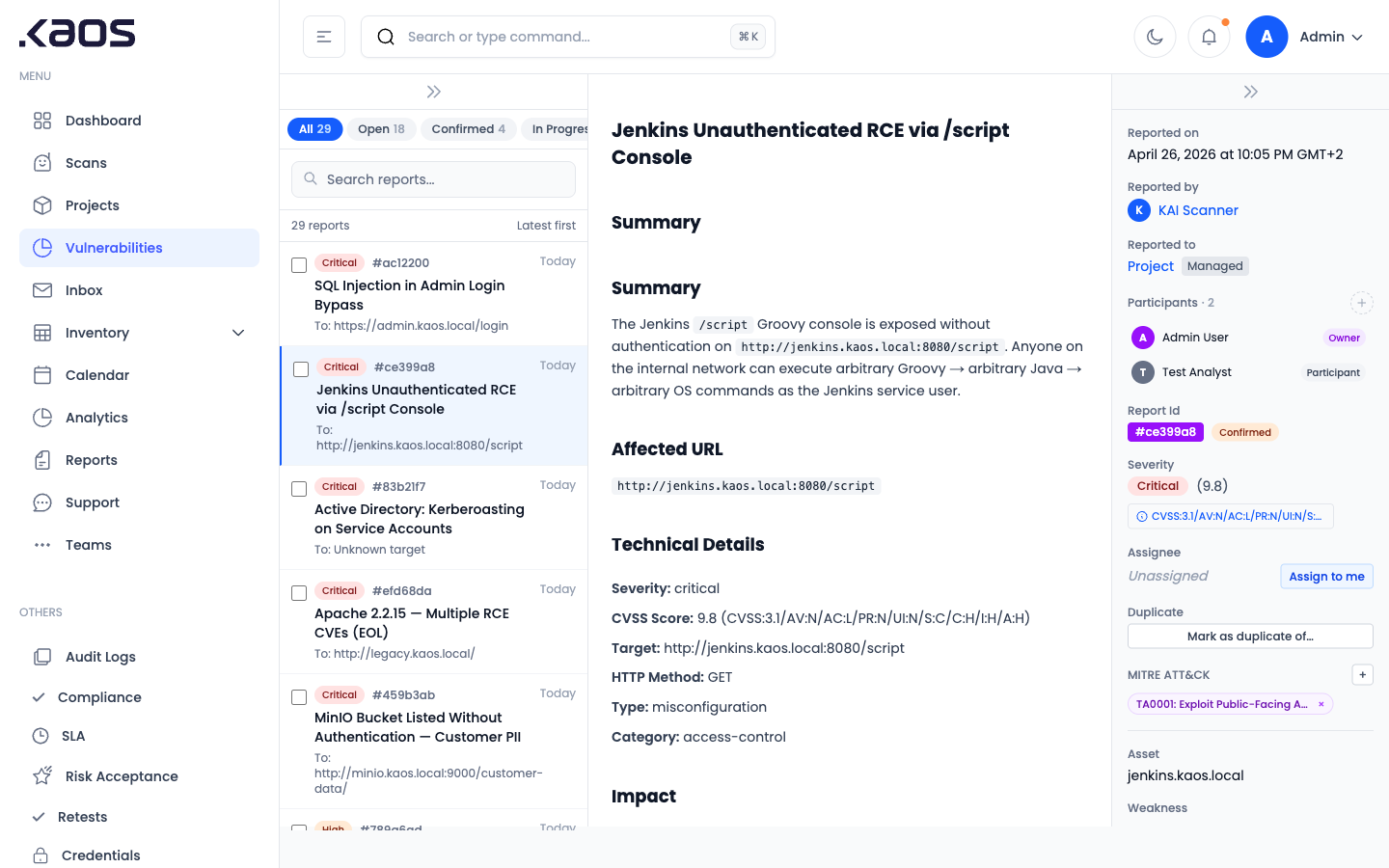
Attack Chain Discovery
Reports Engineering and Execs Trust
Universal Deployment Surface